- [hwsoot] 学习 04/26 03:20
- [游客] 能不能把破解版发我啊?谢谢啊.zjjhfhj@qq.com 05/11 17:35
- [parse] 赞一个! 04/17 20:46
- [游客] 能不能把破解版发我啊?谢谢啊,673856545@qq.com 04/17 13:53
- [游客] 能不能把破解版发我啊?谢谢啊,86738484@qq.com 04/06 21:26
- [游客] 解决了 谢谢~~ 02/24 08:56
- [游客] 怎么解决的呢? 02/24 08:54
- [游客] 能把你破解的版本发给我吗,谢谢.306844939@qq.com 01/18 19:34
- [游客] 通过了,谢谢~~~ 12/06 16:38
- [gsyangchao] 非常不错! 10/09 10:43
- [游客] [url=http://www.gddzbq.com]深圳搬家公司[/url] [url=http 03/02 15:10
- [ewer87] 找到了.PHPmyadmin.. 05/24 14:00
- [ewer87] 请问你在8tt,那个数据库是怎么应用的? 是自己上传么? 为什么传不上去? 不懂。我是第 05/24 13:19
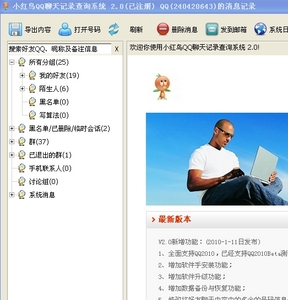
[2010-01-18 15:20] 小红鸟QQ聊天记录查询系统破解
【文章标题】: 小红鸟QQ聊天记录查询系统破解
【文章作者】: 八部天龙
【作者邮箱】: 240420643@qq.com
【作者QQ号】: 240420643
【软件名称】: 小红鸟QQ聊天记录查询系统
【软件大小】: 不知道
【下载地址】: 自己搜索下载
【加壳方式】: 穿山甲
【保护方式】: 无
【编写语言】: vc++
【使用工具】: OD
【操作平台】: XP SP3
【软件介绍】: http://shareware.skycn.com/soft/28045.htm
【作者声明】: 只是感兴趣,没有其他目的。失误之处敬请诸位大侠赐教!
--------------------------------------------------------------------------------
【详细过程】
这个软件唯一的特别之处在于,注册之后仍然会和服务器进行联系,检查是否是正常注册。
开始
用穿山甲脱壳机进行脱壳
双击打开软件,直接出现注册提示框
用OD载入
查找字符串"注册失败,中心返回%s%s",双击来到这里
0042EA80 . E8 BBD70100 CALL dump_.0044C240 ; \dump_.0044C240
0042EA85 . 8985 10FDFFFF MOV DWORD PTR SS:[EBP-2F0],EAX
0042EA8B . 83BD 10FDFFFF>CMP DWORD PTR SS:[EBP-2F0],0
0042EA92 . 0F8E 2F010000 JLE dump_.0042EBC7
0042EA98 . C745 F0 01000>MOV DWORD PTR SS:[EBP-10],1
0042EA9F . 0FB685 03FCFF>MOVZX EAX,BYTE PTR SS:[EBP-3FD]
0042EAA6 . 83F8 01 CMP EAX,1
0042EAA9 0F85 C3000000 JNZ dump_.0042EB72
0042EAAF . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614]
0042EAB5 . E8 9617FFFF CALL dump_.00420250
0042EABA . C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
0042EABE . 8B8D 44FFFFFF MOV ECX,DWORD PTR SS:[EBP-BC]
0042EAC4 . 83C1 74 ADD ECX,74
0042EAC7 . E8 C4CDFEFF CALL dump_.0041B890
0042EACC . 50 PUSH EAX ; /Arg2
0042EACD . 68 BC8C5100 PUSH dump_.00518CBC ; |maccode
0042EAD2 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EAD8 . E8 C31BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EADD . 8D8D 7FFFFFFF LEA ECX,DWORD PTR SS:[EBP-81]
0042EAE3 . 51 PUSH ECX ; /Arg2
0042EAE4 . 68 C48C5100 PUSH dump_.00518CC4 ; |regcode
0042EAE9 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EAEF . E8 AC1BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EAF4 . 8D95 EFFBFFFF LEA EDX,DWORD PTR SS:[EBP-411]
0042EAFA . 52 PUSH EDX ; /Arg2
0042EAFB . 68 CC8C5100 PUSH dump_.00518CCC ; |regtime
0042EB00 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EB06 . E8 951BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EB0B . 8D85 8AFBFFFF LEA EAX,DWORD PTR SS:[EBP-476]
0042EB11 . 50 PUSH EAX ; /Arg2
0042EB12 . 68 D48C5100 PUSH dump_.00518CD4 ; |regmail
0042EB17 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EB1D . E8 7E1BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EB22 . 8B8D 44FFFFFF MOV ECX,DWORD PTR SS:[EBP-BC]
0042EB28 . 83C1 7C ADD ECX,7C
0042EB2B . E8 60CDFEFF CALL dump_.0041B890
0042EB30 . 50 PUSH EAX ; /Arg2
0042EB31 . 68 DC8C5100 PUSH dump_.00518CDC ; |newregcode
0042EB36 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EB3C . E8 5F1BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EB41 . 6A 00 PUSH 0 ; /Arg3 = 00000000
0042EB43 . 6A 00 PUSH 0 ; |Arg2 = 00000000
0042EB45 . 68 E88C5100 PUSH dump_.00518CE8 ; |注册成功!
0042EB4A . E8 F0730500 CALL dump_.00485F3F ; \dump_.00485F3F
0042EB4F . 8B8D 44FFFFFF MOV ECX,DWORD PTR SS:[EBP-BC]
0042EB55 . C781 74030000>MOV DWORD PTR DS:[ECX+374],1
0042EB5F . C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
0042EB63 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614]
0042EB69 . E8 4217FFFF CALL dump_.004202B0
0042EB6E . EB 5C JMP SHORT dump_.0042EBCC
0042EB70 . EB 55 JMP SHORT dump_.0042EBC7
0042EB72 > 8D8D E8F9FFFF LEA ECX,DWORD PTR SS:[EBP-618]
0042EB78 . E8 F3A9FDFF CALL dump_.00409570
0042EB7D . C645 FC 02 MOV BYTE PTR SS:[EBP-4],2
0042EB81 . 68 F88C5100 PUSH dump_.00518CF8 ; /\n\n\n\n如需购买请到软行天下或105商城购买。\n\n付款后,5分钟内你将收到注册码。一次注册,终身使用,免费升级。
0042EB86 . 8D95 04FCFFFF LEA EDX,DWORD PTR SS:[EBP-3FC] ; |
0042EB8C . 52 PUSH EDX ; |Arg3
0042EB8D . 68 608D5100 PUSH dump_.00518D60 ; |注册失败,中心返回%s%s
0042EB92 . 8D85 E8F9FFFF LEA EAX,DWORD PTR SS:[EBP-618] ; |
0042EB98 . 50 PUSH EAX ; |Arg1
0042EB99 . E8 52B6FDFF CALL dump_.0040A1F0 ; \dump_.0040A1F0
0042EB9E . 83C4 10 ADD ESP,10
0042EBA1 . 6A 00 PUSH 0
0042EBA3 . 6A 00 PUSH 0
0042EBA5 . 8D8D E8F9FFFF LEA ECX,DWORD PTR SS:[EBP-618]
0042EBAB . E8 E0CCFEFF CALL dump_.0041B890
0042EBB0 . 50 PUSH EAX ; |Arg1
0042EBB1 . E8 89730500 CALL dump_.00485F3F ; \dump_.00485F3F
0042EBB6 . C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
0042EBBA . 8D8D E8F9FFFF LEA ECX,DWORD PTR SS:[EBP-618]
0042EBC0 . E8 6BAAFDFF CALL dump_.00409630
0042EBC5 . EB 05 JMP SHORT dump_.0042EBCC
0042EBC7 >^ E9 E9FDFFFF JMP dump_.0042E9B5
0042EBCC > 8D8D 24FFFFFF LEA ECX,DWORD PTR SS:[EBP-DC]
0042EBD2 . E8 A9D30100 CALL dump_.0044BF80
0042EBD7 . 837D F0 00 CMP DWORD PTR SS:[EBP-10],0
0042EBDB . 75 0E JNZ SHORT dump_.0042EBEB
0042EBDD . 6A 00 PUSH 0 ; /Arg3 = 00000000
0042EBDF . 6A 00 PUSH 0 ; |Arg2 = 00000000
0042EBE1 . 68 788D5100 PUSH dump_.00518D78 ; |注册信息发送成功,但未收到中心的反馈信息,请多尝试几次或与客服联系!\n\n可通过qq或邮箱联系客服,联系时请将注册序列号和产品注册对话框里的机器码发邮件给xiaohn@400bar.cn。
0042EBE6 . E8 54730500 CALL dump_.00485F3F ; \dump_.00485F3F
0042EBEB > C785 DCF9FFFF>MOV DWORD PTR SS:[EBP-624],0
0042EBF5 . C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
0042EBFC . 8D8D 24FFFFFF LEA ECX,DWORD PTR SS:[EBP-DC]
0042EC02 . E8 C9D20100 CALL dump_.0044BED0
0042EC07 . 8B85 DCF9FFFF MOV EAX,DWORD PTR SS:[EBP-624]
0042EC0D > 8B4D F4 MOV ECX,DWORD PTR SS:[EBP-C]
0042EC10 . 64:890D 00000>MOV DWORD PTR FS:[0],ECX
0042EC17 . 59 POP ECX
0042EC18 . 8B4D EC MOV ECX,DWORD PTR SS:[EBP-14]
0042EC1B . 33CD XOR ECX,EBP
0042EC1D . E8 33170700 CALL dump_.004A0355
0042EC22 . 8BE5 MOV ESP,EBP
0042EC24 . 5D POP EBP
0042EC25 . C2 0400 RETN 4
很明显,下面两个跳转都不能让它跳
0042EA92 . /0F8E 2F010000 JLE dump_.0042EBC7
0042EAA9 /0F85 C3000000 JNZ dump_.0042EB72
这样修改后,我们再来打开一下软件,可以注册成功了,但是过了不到几秒钟,出现“文本字串=系统检测到你的注册信息非法,请重新注册!”
经过我多次尝试,发现情况是这样的:当出现“注册成功”时,所有的限制都解除了,然后跟服务器通信检查注册情况时,发现非法注册,就又出现了限制,所以将下面的代码做如下修改
00449A27 |. 8D8D F4FCFFFF LEA ECX,DWORD PTR SS:[EBP-30C]
00449A2D |. 51 PUSH ECX ; /Arg1
00449A2E |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268] ; |
00449A34 |. E8 D733FCFF CALL dump_.0040CE10 ; \dump_.0040CE10
00449A39 |. 85C0 TEST EAX,EAX
00449A3B |. 75 1E JNZ SHORT dump_.00449A5B ; NOP掉
00449A3D |. 8D95 27FDFFFF LEA EDX,DWORD PTR SS:[EBP-2D9]
00449A43 |. 52 PUSH EDX
00449A44 |. 8D85 9CFDFFFF LEA EAX,DWORD PTR SS:[EBP-264]
00449A4A |. 50 PUSH EAX
00449A4B |. E8 F0750500 CALL dump_.004A1040
00449A50 |. 83C4 08 ADD ESP,8
00449A53 |. 85C0 TEST EAX,EAX
00449A55 |. 0F84 B3000000 JE dump_.00449B0E ; 改成JMP
00449A5B |> 68 E4CE5100 PUSH dump_.0051CEE4 ; /Arg2 = 0051CEE4
00449A60 |. 68 F4CE5100 PUSH dump_.0051CEF4 ; |regcode
00449A65 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C] ; |
00449A6B |. E8 306CFDFF CALL dump_.004206A0 ; \dump_.004206A0
00449A70 |. 837D 08 00 CMP DWORD PTR SS:[EBP+8],0
00449A74 |. 75 0E JNZ SHORT dump_.00449A84
00449A76 |. 6A 00 PUSH 0 ; /Arg3 = 00000000
00449A78 |. 6A 00 PUSH 0 ; |Arg2 = 00000000
00449A7A |. 68 BCCE5100 PUSH dump_.0051CEBC ; |系统检测到你的注册信息非法,请重新注册!
00449A7F |. E8 BBC40300 CALL dump_.00485F3F ; \dump_.00485F3F
00449A84 |> 6A 33 PUSH 33
00449A86 |. 6A 00 PUSH 0
00449A88 |. 8D8D 27FDFFFF LEA ECX,DWORD PTR SS:[EBP-2D9]
00449A8E |. 51 PUSH ECX
00449A8F |. E8 FC630500 CALL dump_.0049FE90
00449A94 |. 83C4 0C ADD ESP,0C
00449A97 |. 6A 33 PUSH 33 ; /Arg3 = 00000033
00449A99 |. 8D95 27FDFFFF LEA EDX,DWORD PTR SS:[EBP-2D9] ; |
00449A9F |. 52 PUSH EDX ; |Arg2
00449AA0 |. 68 F4CE5100 PUSH dump_.0051CEF4 ; |regcode
00449AA5 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C] ; |
00449AAB |. E8 806AFDFF CALL dump_.00420530 ; \dump_.00420530
00449AB0 |. 8D85 27FDFFFF LEA EAX,DWORD PTR SS:[EBP-2D9]
00449AB6 |. 50 PUSH EAX
00449AB7 |. E8 246C0500 CALL dump_.004A06E0
00449ABC |. 83C4 04 ADD ESP,4
00449ABF |. 85C0 TEST EAX,EAX
00449AC1 |. 76 15 JBE SHORT dump_.00449AD8
00449AC3 |. 6A 00 PUSH 0 ; /Arg3 = 00000000
00449AC5 |. 6A 00 PUSH 0 ; |Arg2 = 00000000
00449AC7 |. 68 A8CE5100 PUSH dump_.0051CEA8 ; |系统遭到非法破坏!
00449ACC |. E8 6EC40300 CALL dump_.00485F3F ; \dump_.00485F3F
00449AD1 |. 6A 00 PUSH 0
00449AD3 |. E8 13CE0500 CALL dump_.004A68EB
00449AD8 |> C785 84F9FFFF>MOV DWORD PTR SS:[EBP-67C],0
00449AE2 |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449AE6 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449AEC |. E8 3FFBFBFF CALL dump_.00409630
00449AF1 |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449AF8 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449AFE |. E8 AD67FDFF CALL dump_.004202B0
00449B03 |. 8B85 84F9FFFF MOV EAX,DWORD PTR SS:[EBP-67C]
00449B09 |. E9 A1020000 JMP dump_.00449DAF
00449B0E |> 837D 08 00 CMP DWORD PTR SS:[EBP+8],0
00449B12 |. 74 36 JE SHORT dump_.00449B4A ; NOP掉
00449B14 |. C785 80F9FFFF>MOV DWORD PTR SS:[EBP-680],1
00449B1E |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449B22 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449B28 |. E8 03FBFBFF CALL dump_.00409630
00449B2D |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449B34 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449B3A |. E8 7167FDFF CALL dump_.004202B0
00449B3F |. 8B85 80F9FFFF MOV EAX,DWORD PTR SS:[EBP-680]
00449B45 |. E9 65020000 JMP dump_.00449DAF
00449B4A |> 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449B50 |. E8 DB220000 CALL dump_.0044BE30
00449B55 |. C645 FC 02 MOV BYTE PTR SS:[EBP-4],2
00449B59 |. 68 4D070000 PUSH 74D ; /Arg2 = 0000074D
00449B5E |. 68 8CCE5100 PUSH dump_.0051CE8C ; |222.240.223.82
00449B63 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460] ; |
00449B69 |. E8 F2230000 CALL dump_.0044BF60 ; \dump_.0044BF60
00449B6E |. 85C0 TEST EAX,EAX
00449B70 |. 75 45 JNZ SHORT dump_.00449BB7
00449B72 |. C785 7CF9FFFF>MOV DWORD PTR SS:[EBP-684],1
00449B7C |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449B80 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449B86 |. E8 45230000 CALL dump_.0044BED0
00449B8B |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449B8F |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449B95 |. E8 96FAFBFF CALL dump_.00409630
00449B9A |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449BA1 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449BA7 |. E8 0467FDFF CALL dump_.004202B0
00449BAC |. 8B85 7CF9FFFF MOV EAX,DWORD PTR SS:[EBP-684]
00449BB2 |. E9 F8010000 JMP dump_.00449DAF
00449BB7 |> C785 90F9FFFF>MOV DWORD PTR SS:[EBP-670],0
00449BC1 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449BCB |. C745 F0 00000>MOV DWORD PTR SS:[EBP-10],0
00449BD2 |. 6A 00 PUSH 0 ; /Arg4 = 00000000
00449BD4 |. 68 99000000 PUSH 99 ; |Arg3 = 00000099
00449BD9 |. 8D8D F4FCFFFF LEA ECX,DWORD PTR SS:[EBP-30C] ; |
00449BDF |. 51 PUSH ECX ; |Arg2
00449BE0 |. 68 05100000 PUSH 1005 ; |Arg1 = 00001005
00449BE5 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460] ; |
00449BEB |. E8 80280000 CALL dump_.0044C470 ; \dump_.0044C470
00449BF0 |. 85C0 TEST EAX,EAX
00449BF2 |. 75 45 JNZ SHORT dump_.00449C39
00449BF4 |. C785 78F9FFFF>MOV DWORD PTR SS:[EBP-688],1
00449BFE |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449C02 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449C08 |. E8 C3220000 CALL dump_.0044BED0
00449C0D |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449C11 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449C17 |. E8 14FAFBFF CALL dump_.00409630
00449C1C |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449C23 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449C29 |. E8 8266FDFF CALL dump_.004202B0
00449C2E |. 8B85 78F9FFFF MOV EAX,DWORD PTR SS:[EBP-688]
00449C34 |. E9 76010000 JMP dump_.00449DAF
00449C39 |> C685 04FEFFFF>MOV BYTE PTR SS:[EBP-1FC],0
00449C40 |. 6A 32 PUSH 32
00449C42 |. 6A 00 PUSH 0
00449C44 |. 8D95 05FEFFFF LEA EDX,DWORD PTR SS:[EBP-1FB]
00449C4A |. 52 PUSH EDX
00449C4B |. E8 40620500 CALL dump_.0049FE90
00449C50 |. 83C4 0C ADD ESP,0C
00449C53 |. 68 B1010000 PUSH 1B1
00449C58 |. 6A 00 PUSH 0
00449C5A |. 8D85 37FEFFFF LEA EAX,DWORD PTR SS:[EBP-1C9]
00449C60 |. 50 PUSH EAX
00449C61 |. E8 2A620500 CALL dump_.0049FE90
00449C66 |. 83C4 0C ADD ESP,0C
00449C69 |. C785 90F9FFFF>MOV DWORD PTR SS:[EBP-670],0
00449C73 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449C7D |. 68 88130000 PUSH 1388 ; /Arg4 = 00001388
00449C82 |. 8D8D 90F9FFFF LEA ECX,DWORD PTR SS:[EBP-670] ; |
00449C88 |. 51 PUSH ECX ; |Arg3
00449C89 |. 68 E4010000 PUSH 1E4 ; |Arg2 = 000001E4
00449C8E |. 8D95 04FEFFFF LEA EDX,DWORD PTR SS:[EBP-1FC] ; |
00449C94 |. 52 PUSH EDX ; |Arg1
00449C95 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460] ; |
00449C9B |. E8 A0250000 CALL dump_.0044C240 ; \dump_.0044C240
00449CA0 |. 8945 F0 MOV DWORD PTR SS:[EBP-10],EAX
00449CA3 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449CA9 |. E8 D2220000 CALL dump_.0044BF80
00449CAE |. 837D F0 00 CMP DWORD PTR SS:[EBP-10],0
00449CB2 |. 0F8E B5000000 JLE dump_.00449D6D
00449CB8 |. 0FB685 E3FEFF>MOVZX EAX,BYTE PTR SS:[EBP-11D]
00449CBF |. 83F8 01 CMP EAX,1
00449CC2 |. 74 0C JE SHORT dump_.00449CD0
00449CC4 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449CCE |. EB 0A JMP SHORT dump_.00449CDA
00449CD0 |> C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],1
00449CDA |> 83BD C0FBFFFF>CMP DWORD PTR SS:[EBP-440],0
00449CE1 |. 75 2D JNZ SHORT dump_.00449D10
00449CE3 |. 68 E4CE5100 PUSH dump_.0051CEE4 ; /Arg2 = 0051CEE4
00449CE8 |. 68 F4CE5100 PUSH dump_.0051CEF4 ; |regcode
00449CED |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C] ; |
00449CF3 |. E8 A869FDFF CALL dump_.004206A0 ; \dump_.004206A0
00449CF8 |. 6A 00 PUSH 0 ; /Arg3 = 00000000
00449CFA |. 6A 00 PUSH 0 ; |Arg2 = 00000000
00449CFC |. 68 BCCE5100 PUSH dump_.0051CEBC ; |系统检测到你的注册信息非法,请重新注册!
00449D01 |. E8 39C20300 CALL dump_.00485F3F ; \dump_.00485F3F
00449D06 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449D10 |> 83BD C0FBFFFF>CMP DWORD PTR SS:[EBP-440],0
00449D17 |. 74 54 JE SHORT dump_.00449D6D
00449D19 |. 0FB68D E3FEFF>MOVZX ECX,BYTE PTR SS:[EBP-11D]
00449D20 |. 85C9 TEST ECX,ECX
00449D22 |. 75 49 JNZ SHORT dump_.00449D6D
00449D24 |. 6A 00 PUSH 0
00449D26 |. E8 C0CB0500 CALL dump_.004A68EB
00449D2B |. C785 74F9FFFF>MOV DWORD PTR SS:[EBP-68C],0
00449D35 |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449D39 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449D3F |. E8 8C210000 CALL dump_.0044BED0
00449D44 |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449D48 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449D4E |. E8 DDF8FBFF CALL dump_.00409630
00449D53 |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449D5A |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449D60 |. E8 4B65FDFF CALL dump_.004202B0
00449D65 |. 8B85 74F9FFFF MOV EAX,DWORD PTR SS:[EBP-68C]
00449D6B |. EB 42 JMP SHORT dump_.00449DAF
00449D6D |> 8B95 C0FBFFFF MOV EDX,DWORD PTR SS:[EBP-440]
00449D73 |. 8995 70F9FFFF MOV DWORD PTR SS:[EBP-690],EDX
00449D79 |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449D7D |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449D83 |. E8 48210000 CALL dump_.0044BED0
00449D88 |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449D8C |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449D92 |. E8 99F8FBFF CALL dump_.00409630
00449D97 |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449D9E |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449DA4 |. E8 0765FDFF CALL dump_.004202B0
00449DA9 |. 8B85 70F9FFFF MOV EAX,DWORD PTR SS:[EBP-690]
00449DAF |> 8B4D F4 MOV ECX,DWORD PTR SS:[EBP-C]
00449DB2 |. 64:890D 00000>MOV DWORD PTR FS:[0],ECX
00449DB9 |. 59 POP ECX
00449DBA |. 8B4D EC MOV ECX,DWORD PTR SS:[EBP-14]
00449DBD |. 33CD XOR ECX,EBP
00449DBF |. E8 91650500 CALL dump_.004A0355
00449DC4 |. 8BE5 MOV ESP,EBP
00449DC6 |. 5D POP EBP
00449DC7 \. C3 RETN
不一步一步尝试了,所以就把那些条件跳转给NOP掉!
--------------------------------------------------------------------------------
【经验总结】
没什么经验,只是上星期没有解决,放在这里,今天解决了,坚持不懈吧!!
--------------------------------------------------------------------------------
【版权声明】: 本文原创于看雪技术论坛, 转载请注明作者并保持文章的完整, 谢谢!
2010年01月18日 15:18:33
【文章作者】: 八部天龙
【作者邮箱】: 240420643@qq.com
【作者QQ号】: 240420643
【软件名称】: 小红鸟QQ聊天记录查询系统
【软件大小】: 不知道
【下载地址】: 自己搜索下载
【加壳方式】: 穿山甲
【保护方式】: 无
【编写语言】: vc++
【使用工具】: OD
【操作平台】: XP SP3
【软件介绍】: http://shareware.skycn.com/soft/28045.htm
【作者声明】: 只是感兴趣,没有其他目的。失误之处敬请诸位大侠赐教!
--------------------------------------------------------------------------------
【详细过程】
这个软件唯一的特别之处在于,注册之后仍然会和服务器进行联系,检查是否是正常注册。
开始
用穿山甲脱壳机进行脱壳
双击打开软件,直接出现注册提示框
用OD载入
查找字符串"注册失败,中心返回%s%s",双击来到这里
0042EA80 . E8 BBD70100 CALL dump_.0044C240 ; \dump_.0044C240
0042EA85 . 8985 10FDFFFF MOV DWORD PTR SS:[EBP-2F0],EAX
0042EA8B . 83BD 10FDFFFF>CMP DWORD PTR SS:[EBP-2F0],0
0042EA92 . 0F8E 2F010000 JLE dump_.0042EBC7
0042EA98 . C745 F0 01000>MOV DWORD PTR SS:[EBP-10],1
0042EA9F . 0FB685 03FCFF>MOVZX EAX,BYTE PTR SS:[EBP-3FD]
0042EAA6 . 83F8 01 CMP EAX,1
0042EAA9 0F85 C3000000 JNZ dump_.0042EB72
0042EAAF . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614]
0042EAB5 . E8 9617FFFF CALL dump_.00420250
0042EABA . C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
0042EABE . 8B8D 44FFFFFF MOV ECX,DWORD PTR SS:[EBP-BC]
0042EAC4 . 83C1 74 ADD ECX,74
0042EAC7 . E8 C4CDFEFF CALL dump_.0041B890
0042EACC . 50 PUSH EAX ; /Arg2
0042EACD . 68 BC8C5100 PUSH dump_.00518CBC ; |maccode
0042EAD2 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EAD8 . E8 C31BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EADD . 8D8D 7FFFFFFF LEA ECX,DWORD PTR SS:[EBP-81]
0042EAE3 . 51 PUSH ECX ; /Arg2
0042EAE4 . 68 C48C5100 PUSH dump_.00518CC4 ; |regcode
0042EAE9 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EAEF . E8 AC1BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EAF4 . 8D95 EFFBFFFF LEA EDX,DWORD PTR SS:[EBP-411]
0042EAFA . 52 PUSH EDX ; /Arg2
0042EAFB . 68 CC8C5100 PUSH dump_.00518CCC ; |regtime
0042EB00 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EB06 . E8 951BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EB0B . 8D85 8AFBFFFF LEA EAX,DWORD PTR SS:[EBP-476]
0042EB11 . 50 PUSH EAX ; /Arg2
0042EB12 . 68 D48C5100 PUSH dump_.00518CD4 ; |regmail
0042EB17 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EB1D . E8 7E1BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EB22 . 8B8D 44FFFFFF MOV ECX,DWORD PTR SS:[EBP-BC]
0042EB28 . 83C1 7C ADD ECX,7C
0042EB2B . E8 60CDFEFF CALL dump_.0041B890
0042EB30 . 50 PUSH EAX ; /Arg2
0042EB31 . 68 DC8C5100 PUSH dump_.00518CDC ; |newregcode
0042EB36 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614] ; |
0042EB3C . E8 5F1BFFFF CALL dump_.004206A0 ; \dump_.004206A0
0042EB41 . 6A 00 PUSH 0 ; /Arg3 = 00000000
0042EB43 . 6A 00 PUSH 0 ; |Arg2 = 00000000
0042EB45 . 68 E88C5100 PUSH dump_.00518CE8 ; |注册成功!
0042EB4A . E8 F0730500 CALL dump_.00485F3F ; \dump_.00485F3F
0042EB4F . 8B8D 44FFFFFF MOV ECX,DWORD PTR SS:[EBP-BC]
0042EB55 . C781 74030000>MOV DWORD PTR DS:[ECX+374],1
0042EB5F . C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
0042EB63 . 8D8D ECF9FFFF LEA ECX,DWORD PTR SS:[EBP-614]
0042EB69 . E8 4217FFFF CALL dump_.004202B0
0042EB6E . EB 5C JMP SHORT dump_.0042EBCC
0042EB70 . EB 55 JMP SHORT dump_.0042EBC7
0042EB72 > 8D8D E8F9FFFF LEA ECX,DWORD PTR SS:[EBP-618]
0042EB78 . E8 F3A9FDFF CALL dump_.00409570
0042EB7D . C645 FC 02 MOV BYTE PTR SS:[EBP-4],2
0042EB81 . 68 F88C5100 PUSH dump_.00518CF8 ; /\n\n\n\n如需购买请到软行天下或105商城购买。\n\n付款后,5分钟内你将收到注册码。一次注册,终身使用,免费升级。
0042EB86 . 8D95 04FCFFFF LEA EDX,DWORD PTR SS:[EBP-3FC] ; |
0042EB8C . 52 PUSH EDX ; |Arg3
0042EB8D . 68 608D5100 PUSH dump_.00518D60 ; |注册失败,中心返回%s%s
0042EB92 . 8D85 E8F9FFFF LEA EAX,DWORD PTR SS:[EBP-618] ; |
0042EB98 . 50 PUSH EAX ; |Arg1
0042EB99 . E8 52B6FDFF CALL dump_.0040A1F0 ; \dump_.0040A1F0
0042EB9E . 83C4 10 ADD ESP,10
0042EBA1 . 6A 00 PUSH 0
0042EBA3 . 6A 00 PUSH 0
0042EBA5 . 8D8D E8F9FFFF LEA ECX,DWORD PTR SS:[EBP-618]
0042EBAB . E8 E0CCFEFF CALL dump_.0041B890
0042EBB0 . 50 PUSH EAX ; |Arg1
0042EBB1 . E8 89730500 CALL dump_.00485F3F ; \dump_.00485F3F
0042EBB6 . C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
0042EBBA . 8D8D E8F9FFFF LEA ECX,DWORD PTR SS:[EBP-618]
0042EBC0 . E8 6BAAFDFF CALL dump_.00409630
0042EBC5 . EB 05 JMP SHORT dump_.0042EBCC
0042EBC7 >^ E9 E9FDFFFF JMP dump_.0042E9B5
0042EBCC > 8D8D 24FFFFFF LEA ECX,DWORD PTR SS:[EBP-DC]
0042EBD2 . E8 A9D30100 CALL dump_.0044BF80
0042EBD7 . 837D F0 00 CMP DWORD PTR SS:[EBP-10],0
0042EBDB . 75 0E JNZ SHORT dump_.0042EBEB
0042EBDD . 6A 00 PUSH 0 ; /Arg3 = 00000000
0042EBDF . 6A 00 PUSH 0 ; |Arg2 = 00000000
0042EBE1 . 68 788D5100 PUSH dump_.00518D78 ; |注册信息发送成功,但未收到中心的反馈信息,请多尝试几次或与客服联系!\n\n可通过qq或邮箱联系客服,联系时请将注册序列号和产品注册对话框里的机器码发邮件给xiaohn@400bar.cn。
0042EBE6 . E8 54730500 CALL dump_.00485F3F ; \dump_.00485F3F
0042EBEB > C785 DCF9FFFF>MOV DWORD PTR SS:[EBP-624],0
0042EBF5 . C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
0042EBFC . 8D8D 24FFFFFF LEA ECX,DWORD PTR SS:[EBP-DC]
0042EC02 . E8 C9D20100 CALL dump_.0044BED0
0042EC07 . 8B85 DCF9FFFF MOV EAX,DWORD PTR SS:[EBP-624]
0042EC0D > 8B4D F4 MOV ECX,DWORD PTR SS:[EBP-C]
0042EC10 . 64:890D 00000>MOV DWORD PTR FS:[0],ECX
0042EC17 . 59 POP ECX
0042EC18 . 8B4D EC MOV ECX,DWORD PTR SS:[EBP-14]
0042EC1B . 33CD XOR ECX,EBP
0042EC1D . E8 33170700 CALL dump_.004A0355
0042EC22 . 8BE5 MOV ESP,EBP
0042EC24 . 5D POP EBP
0042EC25 . C2 0400 RETN 4
很明显,下面两个跳转都不能让它跳
0042EA92 . /0F8E 2F010000 JLE dump_.0042EBC7
0042EAA9 /0F85 C3000000 JNZ dump_.0042EB72
这样修改后,我们再来打开一下软件,可以注册成功了,但是过了不到几秒钟,出现“文本字串=系统检测到你的注册信息非法,请重新注册!”
经过我多次尝试,发现情况是这样的:当出现“注册成功”时,所有的限制都解除了,然后跟服务器通信检查注册情况时,发现非法注册,就又出现了限制,所以将下面的代码做如下修改
00449A27 |. 8D8D F4FCFFFF LEA ECX,DWORD PTR SS:[EBP-30C]
00449A2D |. 51 PUSH ECX ; /Arg1
00449A2E |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268] ; |
00449A34 |. E8 D733FCFF CALL dump_.0040CE10 ; \dump_.0040CE10
00449A39 |. 85C0 TEST EAX,EAX
00449A3B |. 75 1E JNZ SHORT dump_.00449A5B ; NOP掉
00449A3D |. 8D95 27FDFFFF LEA EDX,DWORD PTR SS:[EBP-2D9]
00449A43 |. 52 PUSH EDX
00449A44 |. 8D85 9CFDFFFF LEA EAX,DWORD PTR SS:[EBP-264]
00449A4A |. 50 PUSH EAX
00449A4B |. E8 F0750500 CALL dump_.004A1040
00449A50 |. 83C4 08 ADD ESP,8
00449A53 |. 85C0 TEST EAX,EAX
00449A55 |. 0F84 B3000000 JE dump_.00449B0E ; 改成JMP
00449A5B |> 68 E4CE5100 PUSH dump_.0051CEE4 ; /Arg2 = 0051CEE4
00449A60 |. 68 F4CE5100 PUSH dump_.0051CEF4 ; |regcode
00449A65 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C] ; |
00449A6B |. E8 306CFDFF CALL dump_.004206A0 ; \dump_.004206A0
00449A70 |. 837D 08 00 CMP DWORD PTR SS:[EBP+8],0
00449A74 |. 75 0E JNZ SHORT dump_.00449A84
00449A76 |. 6A 00 PUSH 0 ; /Arg3 = 00000000
00449A78 |. 6A 00 PUSH 0 ; |Arg2 = 00000000
00449A7A |. 68 BCCE5100 PUSH dump_.0051CEBC ; |系统检测到你的注册信息非法,请重新注册!
00449A7F |. E8 BBC40300 CALL dump_.00485F3F ; \dump_.00485F3F
00449A84 |> 6A 33 PUSH 33
00449A86 |. 6A 00 PUSH 0
00449A88 |. 8D8D 27FDFFFF LEA ECX,DWORD PTR SS:[EBP-2D9]
00449A8E |. 51 PUSH ECX
00449A8F |. E8 FC630500 CALL dump_.0049FE90
00449A94 |. 83C4 0C ADD ESP,0C
00449A97 |. 6A 33 PUSH 33 ; /Arg3 = 00000033
00449A99 |. 8D95 27FDFFFF LEA EDX,DWORD PTR SS:[EBP-2D9] ; |
00449A9F |. 52 PUSH EDX ; |Arg2
00449AA0 |. 68 F4CE5100 PUSH dump_.0051CEF4 ; |regcode
00449AA5 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C] ; |
00449AAB |. E8 806AFDFF CALL dump_.00420530 ; \dump_.00420530
00449AB0 |. 8D85 27FDFFFF LEA EAX,DWORD PTR SS:[EBP-2D9]
00449AB6 |. 50 PUSH EAX
00449AB7 |. E8 246C0500 CALL dump_.004A06E0
00449ABC |. 83C4 04 ADD ESP,4
00449ABF |. 85C0 TEST EAX,EAX
00449AC1 |. 76 15 JBE SHORT dump_.00449AD8
00449AC3 |. 6A 00 PUSH 0 ; /Arg3 = 00000000
00449AC5 |. 6A 00 PUSH 0 ; |Arg2 = 00000000
00449AC7 |. 68 A8CE5100 PUSH dump_.0051CEA8 ; |系统遭到非法破坏!
00449ACC |. E8 6EC40300 CALL dump_.00485F3F ; \dump_.00485F3F
00449AD1 |. 6A 00 PUSH 0
00449AD3 |. E8 13CE0500 CALL dump_.004A68EB
00449AD8 |> C785 84F9FFFF>MOV DWORD PTR SS:[EBP-67C],0
00449AE2 |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449AE6 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449AEC |. E8 3FFBFBFF CALL dump_.00409630
00449AF1 |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449AF8 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449AFE |. E8 AD67FDFF CALL dump_.004202B0
00449B03 |. 8B85 84F9FFFF MOV EAX,DWORD PTR SS:[EBP-67C]
00449B09 |. E9 A1020000 JMP dump_.00449DAF
00449B0E |> 837D 08 00 CMP DWORD PTR SS:[EBP+8],0
00449B12 |. 74 36 JE SHORT dump_.00449B4A ; NOP掉
00449B14 |. C785 80F9FFFF>MOV DWORD PTR SS:[EBP-680],1
00449B1E |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449B22 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449B28 |. E8 03FBFBFF CALL dump_.00409630
00449B2D |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449B34 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449B3A |. E8 7167FDFF CALL dump_.004202B0
00449B3F |. 8B85 80F9FFFF MOV EAX,DWORD PTR SS:[EBP-680]
00449B45 |. E9 65020000 JMP dump_.00449DAF
00449B4A |> 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449B50 |. E8 DB220000 CALL dump_.0044BE30
00449B55 |. C645 FC 02 MOV BYTE PTR SS:[EBP-4],2
00449B59 |. 68 4D070000 PUSH 74D ; /Arg2 = 0000074D
00449B5E |. 68 8CCE5100 PUSH dump_.0051CE8C ; |222.240.223.82
00449B63 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460] ; |
00449B69 |. E8 F2230000 CALL dump_.0044BF60 ; \dump_.0044BF60
00449B6E |. 85C0 TEST EAX,EAX
00449B70 |. 75 45 JNZ SHORT dump_.00449BB7
00449B72 |. C785 7CF9FFFF>MOV DWORD PTR SS:[EBP-684],1
00449B7C |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449B80 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449B86 |. E8 45230000 CALL dump_.0044BED0
00449B8B |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449B8F |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449B95 |. E8 96FAFBFF CALL dump_.00409630
00449B9A |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449BA1 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449BA7 |. E8 0467FDFF CALL dump_.004202B0
00449BAC |. 8B85 7CF9FFFF MOV EAX,DWORD PTR SS:[EBP-684]
00449BB2 |. E9 F8010000 JMP dump_.00449DAF
00449BB7 |> C785 90F9FFFF>MOV DWORD PTR SS:[EBP-670],0
00449BC1 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449BCB |. C745 F0 00000>MOV DWORD PTR SS:[EBP-10],0
00449BD2 |. 6A 00 PUSH 0 ; /Arg4 = 00000000
00449BD4 |. 68 99000000 PUSH 99 ; |Arg3 = 00000099
00449BD9 |. 8D8D F4FCFFFF LEA ECX,DWORD PTR SS:[EBP-30C] ; |
00449BDF |. 51 PUSH ECX ; |Arg2
00449BE0 |. 68 05100000 PUSH 1005 ; |Arg1 = 00001005
00449BE5 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460] ; |
00449BEB |. E8 80280000 CALL dump_.0044C470 ; \dump_.0044C470
00449BF0 |. 85C0 TEST EAX,EAX
00449BF2 |. 75 45 JNZ SHORT dump_.00449C39
00449BF4 |. C785 78F9FFFF>MOV DWORD PTR SS:[EBP-688],1
00449BFE |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449C02 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449C08 |. E8 C3220000 CALL dump_.0044BED0
00449C0D |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449C11 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449C17 |. E8 14FAFBFF CALL dump_.00409630
00449C1C |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449C23 |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449C29 |. E8 8266FDFF CALL dump_.004202B0
00449C2E |. 8B85 78F9FFFF MOV EAX,DWORD PTR SS:[EBP-688]
00449C34 |. E9 76010000 JMP dump_.00449DAF
00449C39 |> C685 04FEFFFF>MOV BYTE PTR SS:[EBP-1FC],0
00449C40 |. 6A 32 PUSH 32
00449C42 |. 6A 00 PUSH 0
00449C44 |. 8D95 05FEFFFF LEA EDX,DWORD PTR SS:[EBP-1FB]
00449C4A |. 52 PUSH EDX
00449C4B |. E8 40620500 CALL dump_.0049FE90
00449C50 |. 83C4 0C ADD ESP,0C
00449C53 |. 68 B1010000 PUSH 1B1
00449C58 |. 6A 00 PUSH 0
00449C5A |. 8D85 37FEFFFF LEA EAX,DWORD PTR SS:[EBP-1C9]
00449C60 |. 50 PUSH EAX
00449C61 |. E8 2A620500 CALL dump_.0049FE90
00449C66 |. 83C4 0C ADD ESP,0C
00449C69 |. C785 90F9FFFF>MOV DWORD PTR SS:[EBP-670],0
00449C73 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449C7D |. 68 88130000 PUSH 1388 ; /Arg4 = 00001388
00449C82 |. 8D8D 90F9FFFF LEA ECX,DWORD PTR SS:[EBP-670] ; |
00449C88 |. 51 PUSH ECX ; |Arg3
00449C89 |. 68 E4010000 PUSH 1E4 ; |Arg2 = 000001E4
00449C8E |. 8D95 04FEFFFF LEA EDX,DWORD PTR SS:[EBP-1FC] ; |
00449C94 |. 52 PUSH EDX ; |Arg1
00449C95 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460] ; |
00449C9B |. E8 A0250000 CALL dump_.0044C240 ; \dump_.0044C240
00449CA0 |. 8945 F0 MOV DWORD PTR SS:[EBP-10],EAX
00449CA3 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449CA9 |. E8 D2220000 CALL dump_.0044BF80
00449CAE |. 837D F0 00 CMP DWORD PTR SS:[EBP-10],0
00449CB2 |. 0F8E B5000000 JLE dump_.00449D6D
00449CB8 |. 0FB685 E3FEFF>MOVZX EAX,BYTE PTR SS:[EBP-11D]
00449CBF |. 83F8 01 CMP EAX,1
00449CC2 |. 74 0C JE SHORT dump_.00449CD0
00449CC4 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449CCE |. EB 0A JMP SHORT dump_.00449CDA
00449CD0 |> C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],1
00449CDA |> 83BD C0FBFFFF>CMP DWORD PTR SS:[EBP-440],0
00449CE1 |. 75 2D JNZ SHORT dump_.00449D10
00449CE3 |. 68 E4CE5100 PUSH dump_.0051CEE4 ; /Arg2 = 0051CEE4
00449CE8 |. 68 F4CE5100 PUSH dump_.0051CEF4 ; |regcode
00449CED |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C] ; |
00449CF3 |. E8 A869FDFF CALL dump_.004206A0 ; \dump_.004206A0
00449CF8 |. 6A 00 PUSH 0 ; /Arg3 = 00000000
00449CFA |. 6A 00 PUSH 0 ; |Arg2 = 00000000
00449CFC |. 68 BCCE5100 PUSH dump_.0051CEBC ; |系统检测到你的注册信息非法,请重新注册!
00449D01 |. E8 39C20300 CALL dump_.00485F3F ; \dump_.00485F3F
00449D06 |. C785 C0FBFFFF>MOV DWORD PTR SS:[EBP-440],0
00449D10 |> 83BD C0FBFFFF>CMP DWORD PTR SS:[EBP-440],0
00449D17 |. 74 54 JE SHORT dump_.00449D6D
00449D19 |. 0FB68D E3FEFF>MOVZX ECX,BYTE PTR SS:[EBP-11D]
00449D20 |. 85C9 TEST ECX,ECX
00449D22 |. 75 49 JNZ SHORT dump_.00449D6D
00449D24 |. 6A 00 PUSH 0
00449D26 |. E8 C0CB0500 CALL dump_.004A68EB
00449D2B |. C785 74F9FFFF>MOV DWORD PTR SS:[EBP-68C],0
00449D35 |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449D39 |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449D3F |. E8 8C210000 CALL dump_.0044BED0
00449D44 |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449D48 |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449D4E |. E8 DDF8FBFF CALL dump_.00409630
00449D53 |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449D5A |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449D60 |. E8 4B65FDFF CALL dump_.004202B0
00449D65 |. 8B85 74F9FFFF MOV EAX,DWORD PTR SS:[EBP-68C]
00449D6B |. EB 42 JMP SHORT dump_.00449DAF
00449D6D |> 8B95 C0FBFFFF MOV EDX,DWORD PTR SS:[EBP-440]
00449D73 |. 8995 70F9FFFF MOV DWORD PTR SS:[EBP-690],EDX
00449D79 |. C645 FC 01 MOV BYTE PTR SS:[EBP-4],1
00449D7D |. 8D8D A0FBFFFF LEA ECX,DWORD PTR SS:[EBP-460]
00449D83 |. E8 48210000 CALL dump_.0044BED0
00449D88 |. C645 FC 00 MOV BYTE PTR SS:[EBP-4],0
00449D8C |. 8D8D 98FDFFFF LEA ECX,DWORD PTR SS:[EBP-268]
00449D92 |. E8 99F8FBFF CALL dump_.00409630
00449D97 |. C745 FC FFFFF>MOV DWORD PTR SS:[EBP-4],-1
00449D9E |. 8D8D C4FBFFFF LEA ECX,DWORD PTR SS:[EBP-43C]
00449DA4 |. E8 0765FDFF CALL dump_.004202B0
00449DA9 |. 8B85 70F9FFFF MOV EAX,DWORD PTR SS:[EBP-690]
00449DAF |> 8B4D F4 MOV ECX,DWORD PTR SS:[EBP-C]
00449DB2 |. 64:890D 00000>MOV DWORD PTR FS:[0],ECX
00449DB9 |. 59 POP ECX
00449DBA |. 8B4D EC MOV ECX,DWORD PTR SS:[EBP-14]
00449DBD |. 33CD XOR ECX,EBP
00449DBF |. E8 91650500 CALL dump_.004A0355
00449DC4 |. 8BE5 MOV ESP,EBP
00449DC6 |. 5D POP EBP
00449DC7 \. C3 RETN
不一步一步尝试了,所以就把那些条件跳转给NOP掉!
--------------------------------------------------------------------------------
【经验总结】
没什么经验,只是上星期没有解决,放在这里,今天解决了,坚持不懈吧!!
--------------------------------------------------------------------------------
【版权声明】: 本文原创于看雪技术论坛, 转载请注明作者并保持文章的完整, 谢谢!
2010年01月18日 15:18:33
评论次数(6) |
浏览次数(3594) |
类型(加密与解密) |
收藏此文 |
[ bigbigwolf 发表于 2010-01-19 14:04 ]
我也想学破解,先记下 嘿嘿
[ 游客 发表于 2012-01-18 19:34 ]
能把你破解的版本发给我吗,谢谢.306844939@qq.com
[ 游客 发表于 2012-04-06 21:26 ]
能不能把破解版发我啊?谢谢啊,86738484@qq.com
[ 游客 发表于 2012-04-17 13:53 ]
能不能把破解版发我啊?谢谢啊,673856545@qq.com
[ parse 发表于 2012-04-17 20:46 ]
赞一个!
[ 游客 发表于 2012-05-11 17:35 ]
能不能把破解版发我啊?谢谢啊.zjjhfhj@qq.com
